IDA Pro
A powerful disassembler, decompiler and a versatile debugger. In one tool.
A powerful disassembler, decompiler and a versatile debugger. In one tool.

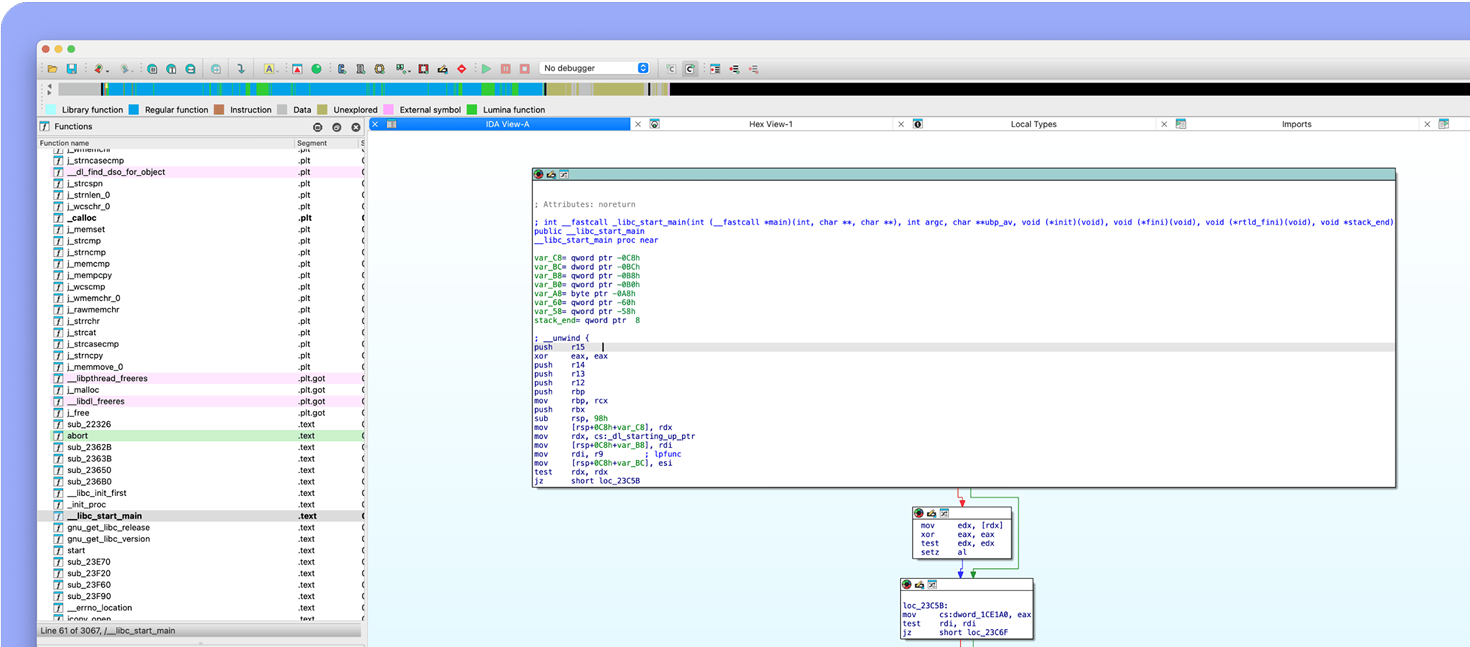
IDA Disassembler excels in supporting various processors and file formats. Its versatility makes it ideal for analyzing embedded systems, mobile apps, or complex software, ensuring you have the best tools for any task.

Automatically obtain a high-quality output, without using IDA’s disassembly manipulation features, e.g. high-level structure definition, naming, typing, commenting, etc...

IDA decompilers focus on delivering code that is readable, maintainable, and semantically similar to the original source code thanks to high-level abstractions, semantic preservation, readability, type inference, structure recovery and more.
Explore IDA Decompilers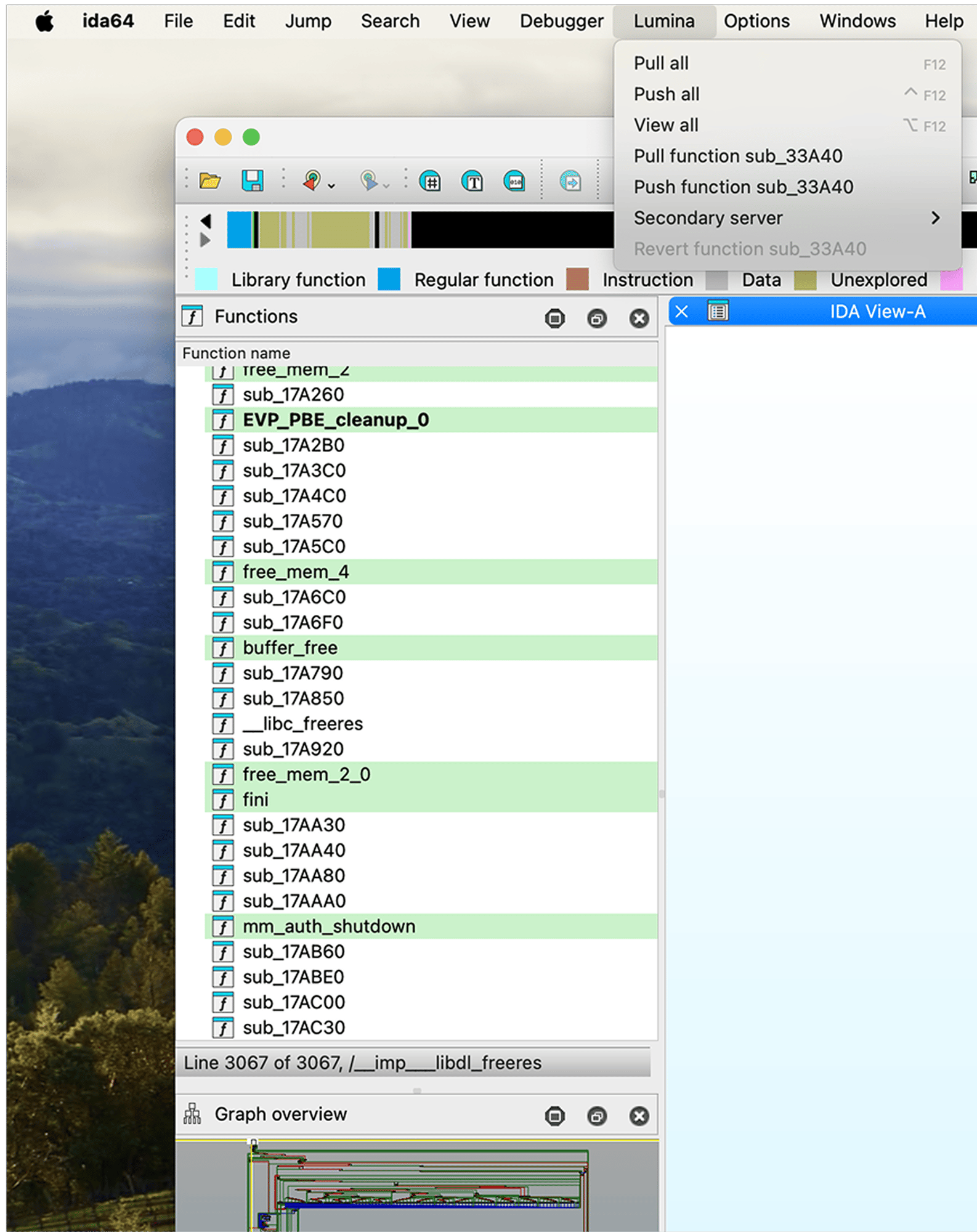
The Public Lumina server by Hex-Rays tracks metadata for functions, like names or operand types. Your IDA instance exchanges only hashes and metadata, avoiding sensitive byte patterns. To control your metadata, enable the Private Lumina add-on for a self-hosted server.
Discover Lumina
We use FLIRT (Fast Library Identification and Recognition Technology) to help reverse engineers identify libraries used in a binary. All to boost the readability of generated disassemblies.
Explore FLIRTSee IDA in action. Kickstart with a lightweight Free
version or pick up a robust IDA Pro.

IDA Pro greatly simplifies the workflow of reverse-engineers dealing with obfuscated binaries, especially those involving Mixed Boolean-Arithmetic (MBA) expressions. The gooMBA plug-in ships with IDA Pro and combines algebraic and program synthesis techniques with smart heuristics for best-in-class deobfuscation performance. It integrates directly into the Hex-Rays decompilers and provides a bridge to an SMT-solver that can prove the correctness of simplifications.
IDA is not only a disassembler but also a versatile debugger. In addition to assisting in error detection and correction within other programs, it supports multiple debugging targets and can handle remote applications.

See IDA in action. Kickstart with a lightweight Free version or pick up a robust IDA Pro.
Boost your knowledge and grow with first-hand guidance from IDA veterans.

If you push to the limit of IDA, you can extend beyond. Develop your own IDA plugin or use the community-crafted ones from our open repository. We cherish the innovative spirit of our user community and hold an annual plugin contest.

IDA Pro comes with a set of tools to enrich your developer experience
⚡️ IDA C++ SDK enables you to develop your own GUI features and much more.
⚡️ IDAPython API helps you create your automation scripts, plug-ins, and more.
⚡️ IDA T makes it possible to run IDA functions from the command line.
⚡️ idalib allows you to run IDA Pro as a library in headless mode.
⚡️ If you opt for the IDA Pro OEM license, you can also use idalib to create derivative works, like embedding idalib into your commercial off-the-shelf software or creating your server applications.
As the complexity of your analysis grows, you may want to use additional tools for enhanced productivity.
Maximize Lumina’s potential with a private server. Secure your data and maintain full control over your metadata.
Collaborate online or offline with your teammates while analyzing the same binary.
macOS 12 (Monterey) or later (x64 or ARM64)
Windows 8 or later (x64)
glibc 2.28, that is Debian 10 / Ubuntu 18.10 / RHEL/CentOS 8 / Fedora 28+ in x86-64 version or ARM64 version
You’ve got questions. We’ve got answers!
No. Once the decompilers are assigned to your license before activation, they cannot be changed during your subscription period. If you upgrade to a higher plan during your subscription period, you will be then prompted to select additional decompilers according to the chosen plan.
Check more details about the decompilers assignment in our FAQ.
Although we currently do not offer the trial version of IDA Pro, we encourage you to try IDA Free to check the basic IDA capabilities.
With IDA Pro plans, we offer three types of licenses to choose from: Named, Computer, or Floating (additional cost).
License availability depends on the plan. For IDA Home and IDA Free plans, only Named licenses are available.
Please refer to the license type details for comparison.
Do you need advice in selecting the right plan or managing your account?